Share this text
Blockchain safety agency CertiK listed three frequent ‘honeypot’ schemes created by exploiters to steal customers’ crypto in decentralized finance (DeFi) in a report titled ‘Honeypot Scams’ revealed on January 11.
Honeypots are misleading schemes focusing on crypto traders and sometimes lure victims with the promise of profitable returns, solely to lure their funds by completely different mechanisms. The alluring worth charts with steady inexperienced candles affect traders’ worry of lacking out (FOMO), resulting in impulsive shopping for. As soon as purchased, these tokens grow to be illiquid as a result of particular mechanisms stopping their sale.
The primary mechanism is labeled by CertiK as ‘The Blacklist’, and its execution consists of stopping customers from promoting rip-off tokens by a lock inserted into the good contract. The report offers an instance by mentioning the ‘_snapshot checklist’ and ‘_snapshotApplied’ capabilities, which let customers transfer tokens. Each of them should be set as ‘True’ within the good contract, in any other case, the person will probably be blocked from transferring funds, appearing as a ‘blacklist’.
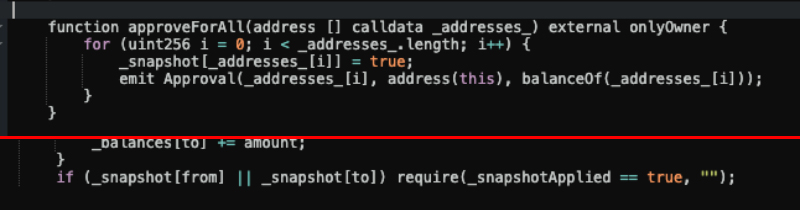
Though the blacklist command could possibly be seen by way of a sensible contract test, CertiK highlights that some blacklists are cleverly hid inside seemingly authentic capabilities, trapping unwary traders.
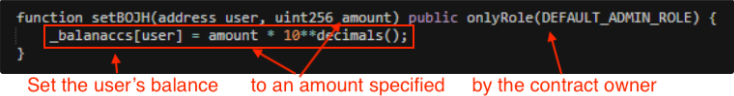
‘Stability Change’ is one other frequent honeypot mechanism utilized by scammers. This system entails altering a person’s token stability to a nominal quantity set by the scammer and it is just readable by the good contract.
Which means that block explorers like Etherscan gained’t replace the stability, and the person gained’t be capable to see that the token quantity was lowered by a big quantity, normally only one token.
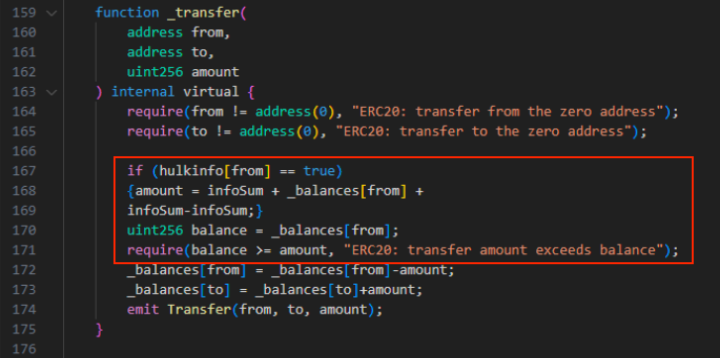
The final frequent tactic utilized by exploiters on DeFi initiatives’ good contracts is the ‘Minimal Promote Quantity’. Though the contract permits customers to promote their tokens, they’ll solely accomplish that when promoting above an unattainable threshold, successfully locking up their funds.
On this case, the person wouldn’t be capable to promote even when the pockets has extra tokens than the edge set. That is due to the operate ‘infosum’ used on this method, which is taken into account on prime of the quantity set to be offered.
For instance, if a person buys 35,000 tokens from a mission through which the good contracts set the promoting threshold to 34,000 utilizing the ‘infosum’ operate, the operation wouldn’t succeed. That’s as a result of the person must promote 35,000 tokens plus the 34,000 set. In different phrases, the 34,000 further tokens requirement might by no means be met.
The influence of honeypots
On prime of the technical facet of honeypot scams, exploiters additionally add a social layer to the scheme, mimicking respected crypto initiatives to deceive traders. Furthermore, dangerous actors devised a option to automate the creation of honeypots. CertiK’s report mentions a pockets liable for creating rip-off contracts each half-hour over two months. In whole, 979 contracts linked to this service had been recognized.
If a mean of $60 was stolen, which is a reasonably small quantity in comparison with bigger scams on DeFi, roughly $59,000 could be taken from customers over two months. In response to CertiK, this turns “vigilance and training” into an pressing matter in DeFi.






